Cylera labs recently researched and published their study on a “flaw” in the DICOM image format for communication of medical imaging information could be exploited to hide malware in MRI and CT scans alongside other patient data. This weakness in the DICOM image file format, if exploited, enables malware to infect patient data by directly inserting itself into medical imaging files. However, The report does not show that there has been any incident where the flaw actually exploited. This weakness in DICOM allows malware to become ePHI without affecting its ability to function. Removal of this malware (delete or quarantine) may also result in inadvertently deleting patient information or compromise the availability of the clinical information. The DICOM standard is used by medical devices that produce imagery for CT and MRI machines; specialized workstations for analyzing scan results; and even phones and tablets used to view diagnostic information. Antivirus solutions should update to make their products PE/DICOM-aware, with custom detection and containment mechanisms that don’t leak or delete ePHI. Telegenisys is a HIPAA compliant organization, where we ensure that our antivirus and anti-malware tools are updated for the latest threats. Know more about HIPAA security
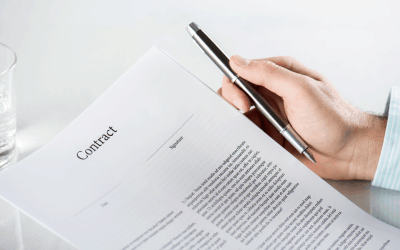
HIPAA: When are business associates directly liable to safeguard PHI
The HHS office for civil rights (OCR) issued the last standard in 2013 to adjust the HIPAA privacy, Security, Breach...








0 Comments